1. A wireless client is attempting to establish a connection with a wireless access point. What process does the client use to discover the access points which are available to it?
probing
beaconing
association
authentication
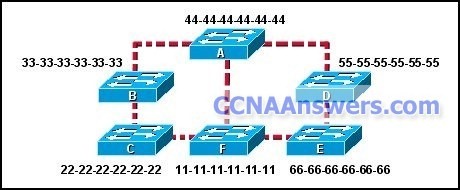
2.
Refer to the exhibit. Each switch is shown with its MAC address. Which switch will be elected as the spanning-tree root bridge if the switches are configured with their default priority values?
switch A
switch B
switch C
switch D
switch E
switch F
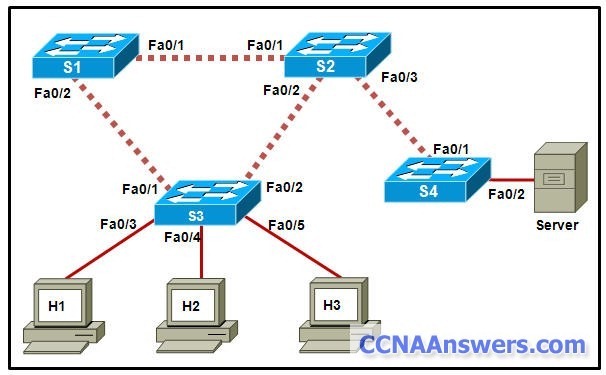
3.
Refer to the exhibit. Which two switch interfaces would be RSTP edge ports? (Choose two.)
switch S1, Fa0/1
switch S3, Fa0/5
switch S4, Fa0/1
switch S2, Fa0/3
switch S4, Fa0/2
switch S3, Fa0/2
4. What is a function or characteristic of the native VLAN?
It is the VLAN that supports untagged traffic on an 802.1Q trunk.
It is always assigned to VLAN 1 for backward compatibility.
It is always the same VLAN number for all trunks within an organization.
It is used as the management VLAN throughout the entire switched network.
5. A network administrator must purchase new access layer switches to deploy across an existing hierarchical network that supports voice and data traffic. At a minimum, which two features should the new access layer switches support? (Choose two.)
PoE
QoS
modular design
Layer 3 support
line speed forwarding rates
6. Which combination is required to establish a connection to initially configure the Linksys WRT300N wireless access device?
a computer with a console connection to the WRT300N
a computer with a wireless connection to the WRT300N
a computer with an AUX port connection to the WRT300N
a computer configured in the same IP subnet as the WRT300N and a direct cable connection to it
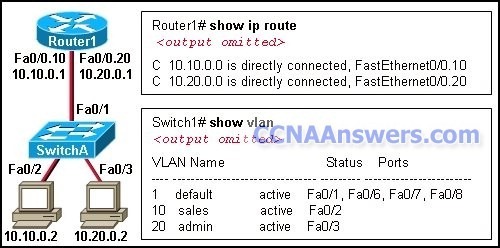
7.
Refer to the exhibit. A network administrator has segmented the network into two VLANs and configured Router1 for inter-VLAN routing. A test of the network, however, shows that hosts on each VLAN can only access local resources and not resources on the other VLAN. What is the most likely cause of this problem?
Switch port Fa0/1 is not trunking.
Router interface Fa0/0 is possibly down.
No routing protocol is configured on Router1.
One of the router subinterfaces is possibly down.
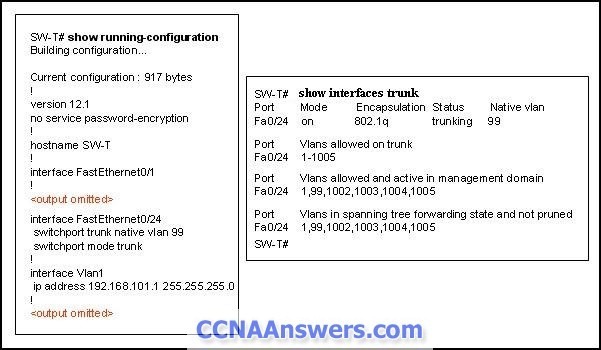
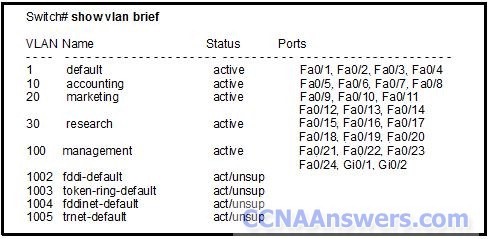
8.
Refer to the exhibit. SW-T has been configured with a single trunking interface. Which VLANs will be allowed across the trunk?
Only VLAN 1 will be allowed across the trunk.
All configured VLANs will be allowed across the trunk.
Only the native VLAN will be allowed across the trunk.
Only the the management and native VLANs will be allowed across the trunk.
Only VLANs that are configured on the VTP server in the domain will be allowed across the trunk.
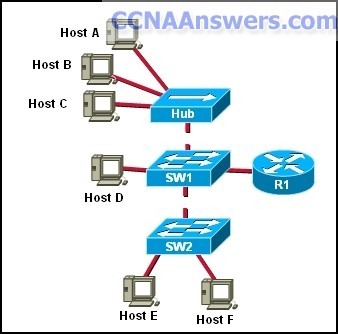
9.
Refer to the exhibit. Hosts B and C attempt to transmit a frame at the same time, but a collision occurs. Which hosts will receive the collision jamming signal?
all hosts that are shown
only hosts B and C
only hosts A, B, and C
only hosts A, B, C, and D
only hosts A, D, E, and F
only hosts D, E, and F
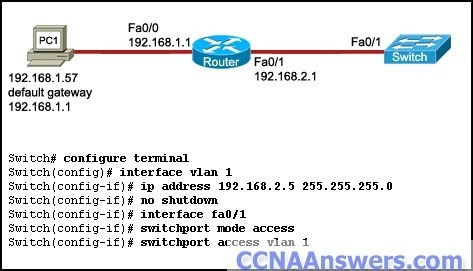
10.
Refer to the exhibit. The switch VTY lines have been properly configured, but PC1 is unable to remotely manage the switch. How can this problem be resolved?
Configure the Fa0/1 interface of the switch in trunk mode.
Configure a default gateway on the switch.
Configure the native VLAN on the switch.
Configure the Fa0/1 interface of the switch to allow all VLANs.
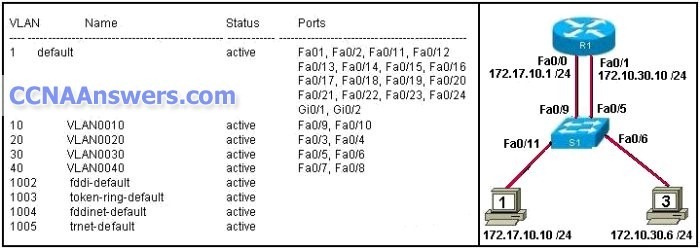
11.
Refer to the exhibit. R1 is configured for traditional inter-VLAN routing. R1 can ping computer 3 but cannot ping computer 1. What is a possible cause for this failure?
S1 port Fa0/11 is in the wrong VLAN.
R1 does not have an active routing protocol.
The IP address of computer 1 is in the wrong logical network.
Router interface Fa0/0 has the wrong trunk encapsulation type configured.
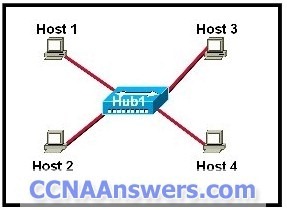
12.
Refer to the exhibit. All hosts are in listen mode. Host 1 and Host 4 both transmit data at the same time. How do the hosts respond on the network? (Choose two.)
After the end of the jam signal, a backoff algorithm is invoked.
Hosts 1 and 4 are operating full duplex so no collision will exist.
The hub will block the port connected to Host 4 to prevent a collision.
Hosts 1 and 4 are assigned shorter backoff values to provide them priority to access the media.
If a host has data to transmit after the backoff period of that host, the host checks to determine if the line is idle before transmitting.
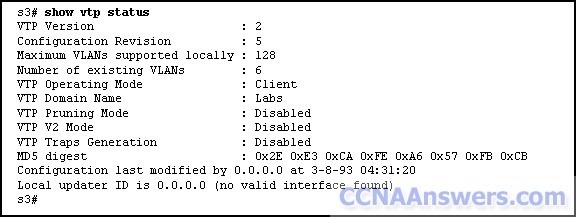
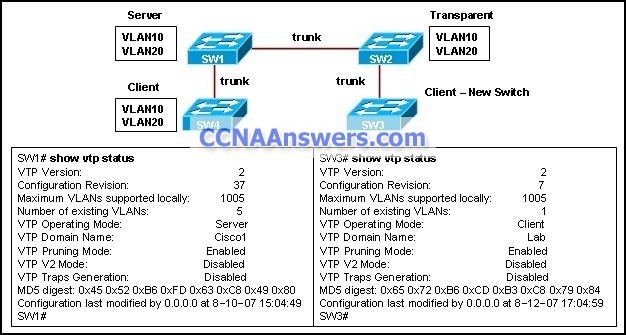
13.
Refer to the exhibit. The network administrator is planning five additional VLANs to be shared throughout the VTP domain on S3. What action should the administrator take before creating the additional VLANs?
Create the VLANs on a switch in VTP server mode and allow them to propogate to the other switches in the domain.
Modify the configuration revision to 10 to support the additional VLANs.
Enable the VTP pruning mode in order to create the VLANs on S3.
Enable the VTP v2 mode.
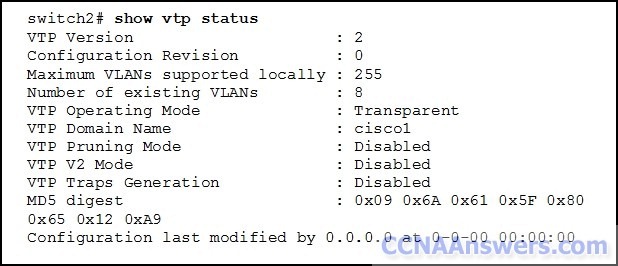
14.
Refer to the exhibit. Which two settings show the default value of VTP configuration on a Cisco 2960 switch? (Choose two.)
revision number
existing VLANs
operating mode
domain name
pruning mode
15. An administrator is troubleshooting a PC on the network which is suffering from slow and intermittent connectivity. The PC has a ping success rate to the default gateway of less than half the ping attempts. Other PCs on the switch can consistently ping the default gateway. The switch port is configured for auto duplex and the PC is configured for full duplex. What will commonly cause this problem?
The PC is set to full duplex. The switch port fails to autonegotiate the duplex setting and defaults to half duplex, which causes a duplex mismatch.
The switch traffic is exceeding available frame buffers. The result is that frames are being dropped.
The PC and the default gateway have different bandwidth Ethernet ports.
The default gateway is not on the same switch that the PC is.
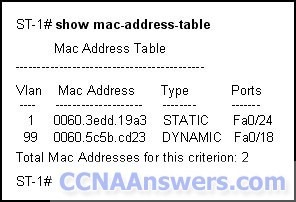
16.
Refer to the exhibit. What does the term DYNAMIC indicate in the output that is shown?
This entry can only be removed from the MAC address table by a network administrator.
When forwarding a frame to the device with address 0060.5c5b.cd23, the switch does not have to perform a lookup to determine the final destination port.
Only the device with MAC address 0060.5c5b.cd23 will be allowed to connect to port Fa0/18.
The switch learned this MAC address from the source address in a frame received on Fa0/18.
17. Which switching method provides error-free data transmission?
fragment-free
fast-forward
integrity-checking
store-and-forward
18. Which wireless topology supports roaming from one access point to another?
ESS
BSS
IBSS
ad hoc
19. Which value determines if a switch becomes the central point of reference in the spanning tree topology?
lowest bridge ID
highest revision number
lowest numeric IP address
highest numeric MAC address
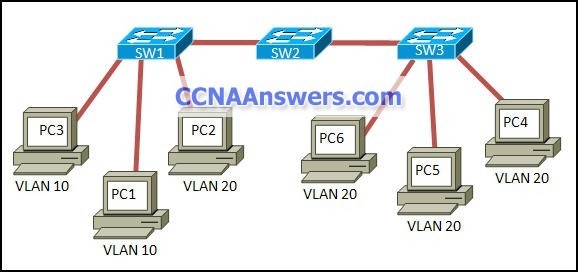
20.
Refer to the exhibit. The broadcast traffic from PC1 is consuming bandwidth on the interswitch trunks. What should be done to prevent this from happening?
Move PC1 to a port on SW3.
Move PC2 to a port on SW3.
Move PC1 to a port on SW2.
Enable pruning for VLAN10 on the VTP server.
Associate PC1 as a member of a new VLAN.
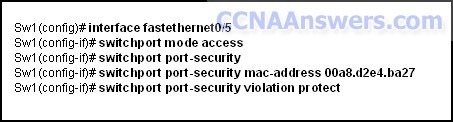
21.
Refer to the exhibit. What happens when a frame from a source MAC address different from 00a8.d2e4.ba27 reaches switch port 0/5?
The frame is dropped.
The port is shut down.
An error message is displayed.
FastEthernet port 0/5 will show an err-disabled message.
22. A wireless access point is configured for WPA2. Which encryption algorithm will all devices that connect to the access point be required to use?
AES
PPK
PSK
TKIP
WEP
23. Where is the information of newly created VLANs stored on a switch?
CPU
flash
NVRAM
RAM
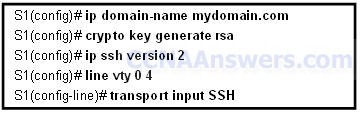
24.
Refer to the exhibit. The configuration steps that are listed in the exhibit have been entered in switch S1 via the console. Subsequent attempts to telnet to the switch are not successful. What is causing the problem?
The switch must be configured with SSH version 1.
The transport input command must specify Telnet access.
The RSA keys must be returned to zero before SSH will permit Telnet access.
The ip domain-name command must also be entered in line configuration mode for the vty lines.
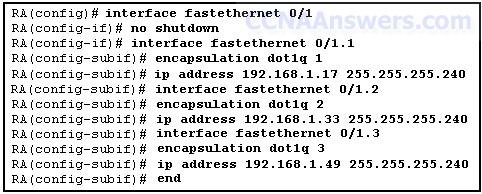
25.
Refer to the exhibit. A new host needs to be connected to VLAN 1. Which IP address should be assigned to this new host?
192.168.1.11 /28
192.168.1.22 /28
192.168.1.33 /28
192.168.1.44 /28
192.168.1.55 /28
26.
Refer to the exhibit. A new switch, SW3, has been added to the network. The network administrator determines that VLAN information is not propagating to SW3. Which command will remedy the problem?
SW1(config)# vtp version 1
SW2(config)# vtp mode client
SW3(config)# vtp domain Cisco1
SW3(config)# vtp mode transparent
27. Which STP port type can only appear once on a segment, and must be present in order for traffic to flow on that segment?
non-root port
disabled port
designated port
non-designated port
28. What is one disadvantage that 802.11a wireless has compared to 802.11g?
Use of the 5GHz band requires much larger antennas.
The OFDM modulation technique results in a slower data rate.
There are fewer non-overlapping channels available to help reduce RF interference.
The use of higher frequencies means that signals are more likely to be obstructed.
29. Why is MAC address filtering considered a poor choice in securing a WLAN?
Available bandwidth is reduced.
MAC addresses are easily spoofed.
APs are more susceptible to DoS attacks.
The payload encryption is easily broken.
30. What is the purpose of the Spanning Tree algorithm?
It propagates VLAN configurations to other switches.
It restricts broadcast packets to a single VLAN.
It segments a network into multiple broadcast domains.
It prevents loops in a switched network with redundant paths.
31. What are two benefits of a hierarchical network model over a flat network design? (Choose two.)
reduced cost of equipment
increased network availability
elimination of equipment downtime
reduced size of the physical network layout
simplification of management and troubleshooting
elimination of the need for Layer 3 functionality
32. What is the purpose of VLAN trunking?
It improves network performance by reducing broadcast traffic.
It selects the best path to transmit data in a switched network.
It carries the traffic of multiple VLANs through a single link.
It avoids spanning tree loops in a switched network.
33. Which two statements describe the operation of an access layer Ethernet switch? (Choose two.)
Broadcasts are natively blocked by the switch.
Subnetting is used by the switch to segment local networks.
Frames that contain an unknown destination MAC address are dropped by the switch.
The source MAC address within a frame is used by the switch to associate a port with that MAC address.
Frames are directed by the switch from one port to another based on the destination MAC address within the frame.
Data packets are forwarded by the switch from one port to another based on the destination IP address within the packet.
34. Which two types of traffic are always transmitted as untagged frames? (Choose two.)
traffic that is assigned to the default VLAN
traffic that is assigned to the native VLAN
traffic from the voice VLAN on an IP phone
Telnet, HTTP, or SSH traffic for switch management
traffic that is leaving an access mode port that is connected to another switch
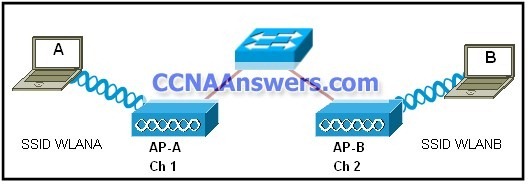
35.
Refer to the exhibit. Users A and B are reporting intermittent connectivity problems. Pre-installation surveys showed strong signal strength from the AP locations to the client locations. Outside electrical interference has been eliminated. What will fix the problem?
Relocate the APs closer to each other.
Increase the distance between the clients.
Change the channel on AP-B to 6 or 11.
Place AP-A and AP-B on the same wireless channel.
36. Which statement correctly describes a function of a Layer 2 switch?
It routes packets between different LAN segments.
It uses the destination MAC address to selectively forward a frame.
It performs switching and filtering based on the destination network layer address.
It drops a frame whose destination MAC address is not in the MAC address table.
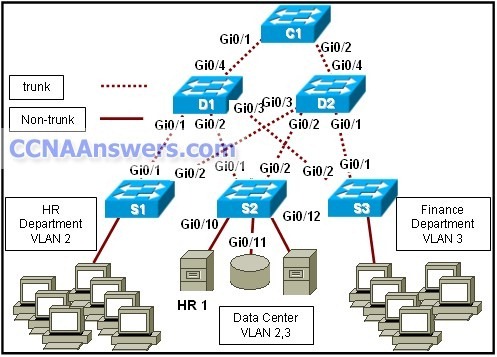
37.
Refer to the exhibit. The Layer 2 switching design that is shown has been implemented in a campus environment that is using Spanning Tree Protocol. All inter-switch links that are shown are trunks. Whenever an inter-switch link fails, the network takes nearly a minute to completely converge. How can the convergence time be reduced?
Increase the capacity of the distribution and core trunk links to 10 Gb/s.
Add a trunk link that directly connects D1 and D2.
Use Layer 3 switching on the core switch.
Implement Rapid Spanning Tree Protocol.
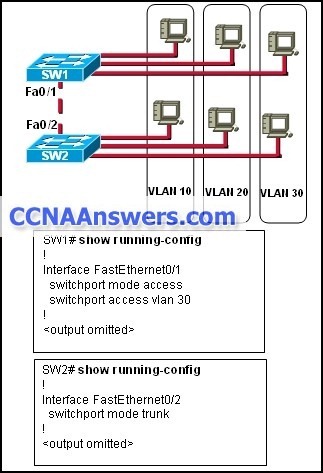
38.
Refer to the exhibit. Hosts that are connected to switch SW1 are not able to communicate with hosts in the same VLAN that are connected to switch SW2. What should be done to fix the problem?
Introduce a Layer 3 device in the topology.
Configure both switches in VTP transparent mode to allow them to share VLAN information.
Reconfigure the fa0/1 interface on switch SW1 with a static trunk configuration.
Apply IP addresses that are in the same subnet to FastEthernet 0/1 on SW1 and FastEthernet 0/2 on SW2.
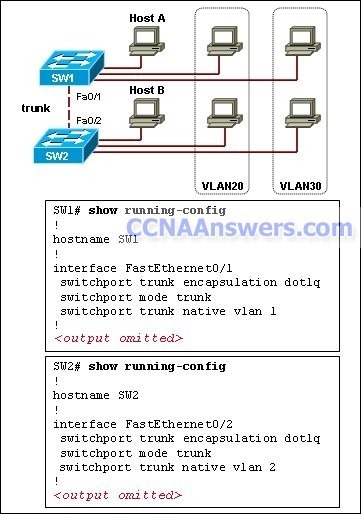
39.
Refer to the exhibit. Both switches are interconnected via a trunk link. Host A and host B are on the default VLAN but are not able to exchange traffic. What should be done to fix the problem?
Allow all VLANs on the trunk link.
Remove the native VLAN from the trunk.
Include a router or switch with Layer 3 capabilities.
Configure the same native VLAN on both ends of the trunk.
40.
Refer to the exhibit. What is the maximum number of VLANs that can be deleted from the Switch as it is configured?
zero
four
five
eight
nine
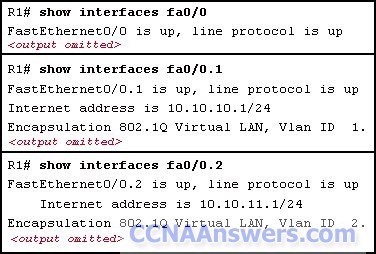
41.
Refer to the exhibit. Which two statements are true about the operation of the interfaces? (Choose two.)
Incoming traffic with VLAN ID 0 is processed by interface fa0/0.
Incoming traffic that has a VLAN ID of 2 is processed by subinterface fa0/0.2.
Both subinterfaces remain up with line protocol up, even if fa0/0 line protocol is down.
Subinterfaces use unique MAC addresses by adding the 802.1Q VLAN ID to the hardware address.
Traffic inbound on this router is processed by different subinterfaces, depending on the VLAN from which the traffic originated.
42. What is the benefit of the auto-MDIX feature on a Cisco Catalyst switch?
dynamically assigns a new management VLAN ID
autonegotiates IP address information for initial management connections
allows the use of straight-through patch cables regardless of connected device types
places a port immediately in the forwarding state to reduce the time for the spanning tree to reconverge
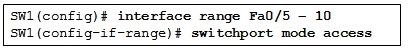
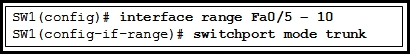
43. A network technician is attempting to configure 802.1q trunking on switch ports Fa0/5 through Fa0/10. Which set of commands will accomplish this task?
44. What can an administrator do to ensure that a specific switch will win a root election if all switches are set to their default configurations?
Set the bridge priority to 16384.
Change the VTP mode to server.
Assign a port priority of 128 for all ports on the switch.
Configure a loopback interface with the highest IP address.
45. Why is it advisable that a network administrator use SSH instead of Telnet when managing switches?
SSH uses TCP whereas Telnet does not.
SSH encrypts only the username and password when logging in.
SSH encrypts all remote management communications whereas Telnet does not.
SSH sends a clear text message steam which reduces the bandwidth use for management.
46. What will be the effect of the command S1# copy system:running-config tftp://172.16.2.155/tokyo-config?
The IOS will be copied to the TFTP server.
The configuration file named tokyo-config will overwrite the startup configuration file on S1.
The running configuration file on S1 will be saved via TFTP to a file named tokyo-config.
The contents of NVRAM on S1 will become the startup configuration file on the tokyo switch.
47. What is the purpose of the switch command switchport access vlan 99?
to enable port security
to make the port operational
to assign the port to a particular VLAN
to designate the VLAN that does not get tagged
to assign the port to the native VLAN (VLAN 99)
48. Which Cisco switch feature is used to limit the number of valid MAC addresses that a switch associates with a switchport?
VLANs
PortFast
port security
VTP pruning
DHCP snooping
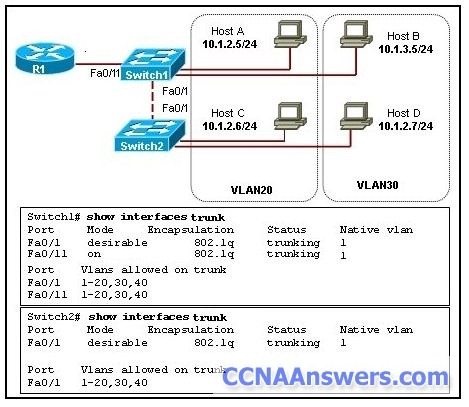
49.
Refer to the exhibit. The devices in the network are operational and configured as indicated in the exhibit. However, hosts B and D cannot ping each other. What is the most likely cause of this problem?
The link between the switches is up but not trunked.
The Fa0/11 interface of Switch1 is not configured as a trunk.
Hosts B and D are configured with IP addresses from different subnets.
VLAN 20 and VLAN 30 are not allowed on the trunk between the switches.
50. Which two statements describe VTP transparent mode operation? (Choose two.)
Transparent mode switches can create VLAN management information.
Transparent mode switches can add VLANs of local significance only.
Transparent mode switches pass any VLAN management information that they receive to other switches.
Transparent mode switches can adopt VLAN management changes that are received from other switches.
Transparent mode switches originate updates about the status of their VLANS and inform other switches about that status.
51. RSTP is enabled in a switched network that is active and converged. Which switch port type assumes a discarding state on non-root switches?
root port
edge port
alternate port
designated port
52. The network administrator wants to configure a switch to pass VLAN update information to other switches in the domain but not update its own local VLAN database. Which two steps should the administrator perform to achieve this? (Choose two.)
Reset the VTP counters.
Configure VTP version 1 on the switch.
Configure the VTP mode of the switch to transparent.
Verify that the switch has a higher configuration revision number.
Configure the switch with the same VTP domain name as other switches in the network.
credit to : ccnaanswers.com